📣 Since our article, Uber’s official blog has addressed the incident
Is Uber struggling with security? #
To begin our investigation, we started by looking into the company’s history of security breaches. Here is a brief summary.
2014 #
Leak of a token on a public GitHub repository that allowed access to a database containing the data of 100,000 drivers.
2016 #
The data of 600,000 American drivers and 57 million users of the company’s services were stolen. Subsequently, the company attempted to buy the silence of the hackers and the destruction of the data they collected for $100,000.
2020 #
Former Uber security chief Joe Sullivan is prosecuted by the US justice system for obstruction of justice regarding the 2016 breach.
Cybersecurity researchers discover a dataset containing the credentials and personal information of 579 users and 100 Uber Eats drivers.
2022 #
Uber is shaken by the publication of investigations conducted by several newspapers under the name Uber files. The files used in the investigation were obtained from a former lobbyist of the group who stole no less than 124,000 internal documents. The emails of executives, presentations, notes, and invoices were found in the files.
A Troubled History #
Through its complicated history, Uber seems to have a strained relationship with the concept of protecting user data. Concerns arise from practices that flirt with illegality.
- Attempted purchase of hackers outside legal boundaries and without guarantee of success
- Massive email theft by a lobbyist with no technical skills and without being detected
This raises questions about the integrity of the information system and compliance with regulations governing the use of personal data.
What happened during the hack? #
On September 15, 2022, social media erupted with the publication of this New York Times article.
It revealed that a hacker was roaming the information system, supported by screenshots of administration consoles.
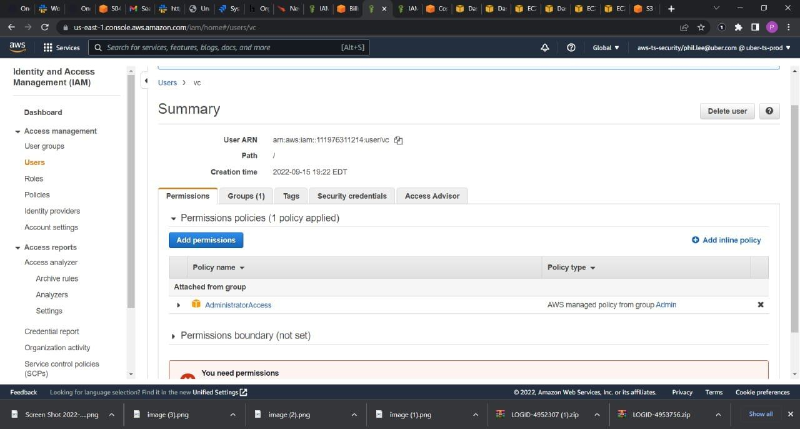
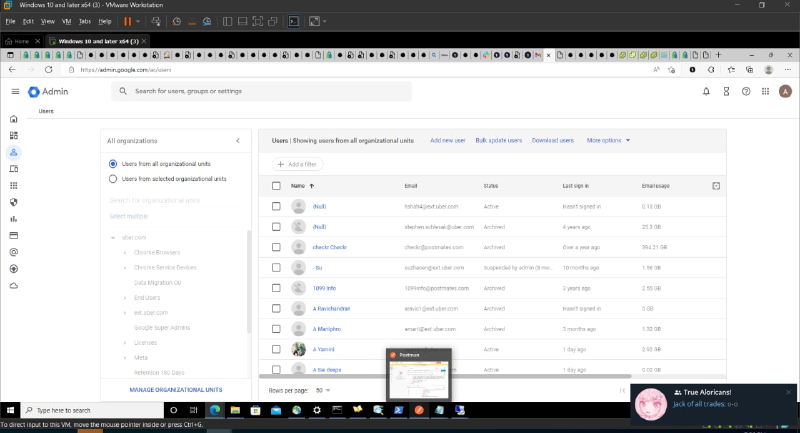
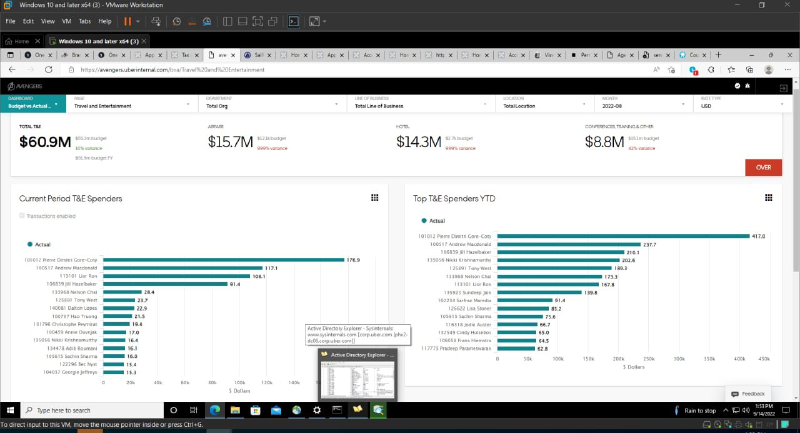
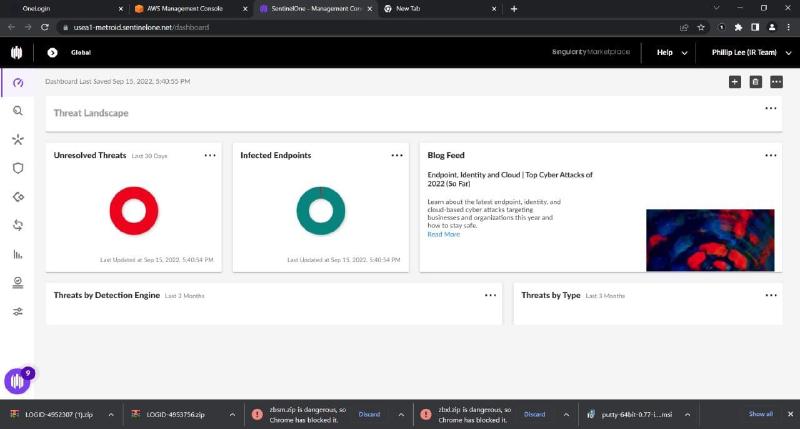
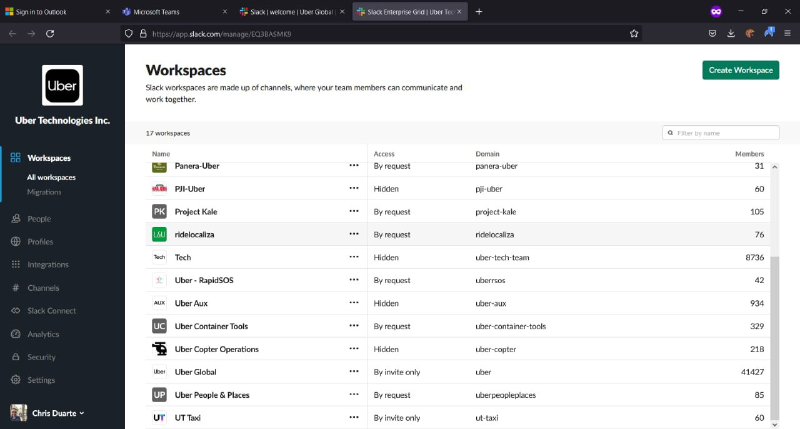
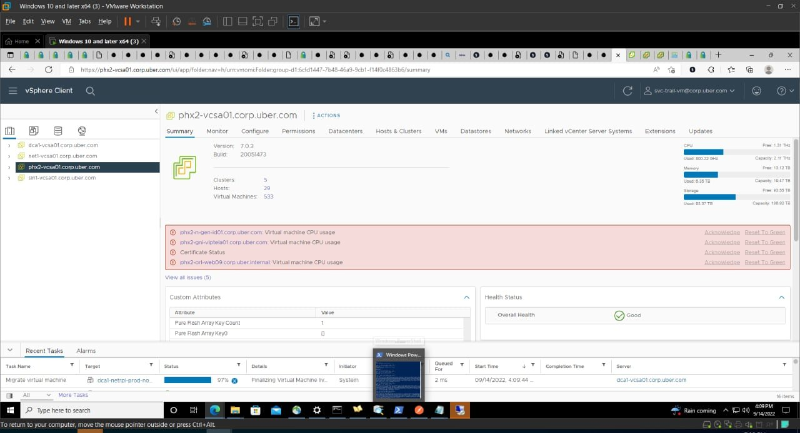
Screenshots shared by the hacker
The hacker presents himself as an 18-year-old who managed to penetrate the fortress using a social engineering technique. However, few details about the technique in question are revealed.
He later contacted Uber’s teams, announcing that he had compromised the company’s security.

Initially taken as a joke, an internal email asking employees to remain silent eventually raised doubts.
The next day, after an initial statement confirming the investigation, the company stated that no access to user data had been detected and that internal services were back online.
What is the impact on the IS? #
By analyzing the images, we discover that the hacker has full access to the company’s information system. We can thus list the services to which they may have had access.
- AWS and Vsphere Console - Access to servers and virtual machines
- Confluence Console - Access to internal documentation
- HackerOne Account - Access to confidential information about the latest vulnerabilities reported to the platform (Bug Bounty)
- SentinelOne Console - Access to the administration panel of workstation antivirus
- Slack Console - Access to internal messaging
- GSuite Console - Access to internal documents, emails, calendars
It is worth noting the large amount of documents hosted on the Google suite. Nearly 1.11 petabits of data.
Some employees have reported the interruption of certain internal services, but the intrusion did not cause any service interruptions.
The Recipe #
One of the most obscure aspects of this story is how the hacker managed to break into the computer system.
Into the Darknet #
Several sources who analyzed the screenshots shared by the hacker agree that the hacker may have purchased the login credentials of an Uber employee on the darknet a few days before the attack.

The hacker’s downloads include log files sold on illegal platforms. They come from malware (Raccoon and Vidar) deployed by other hacking groups that have infected computers and exfiltrated login data.
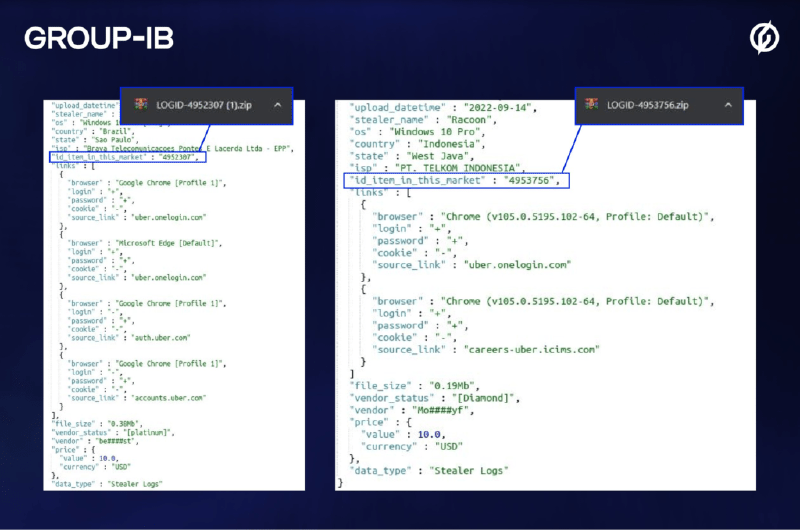
Analysis of the logs purchased by the hacker
In this last image, Group-IB purchased the same samples as the hacker to verify their contents. It very explicitly contains credentials to access Uber’s authentication platform.
Social Engineering? #
Uber, like many large companies, uses a method of two-factor authentication. Therefore, the hacker cannot log in with these credentials.
We assume that it was at this point that the hacker resorted to a social engineering method. Several rumors explain that he managed to impersonate someone from the IT department and succeeded in adding his phone as a trusted source. This way, he could generate codes that gave him full access to the employee’s account.
Other popular techniques exist, such as spamming the user with approval requests until they accept.
Secret, where are you hiding? #
Once access was obtained, the hacker would have connected to the company’s VPN and started scanning the internal network. On this network, they would have discovered a collection of PowerShell scripts, one of which contained admin credentials for the Thycotic (PAM) tool.
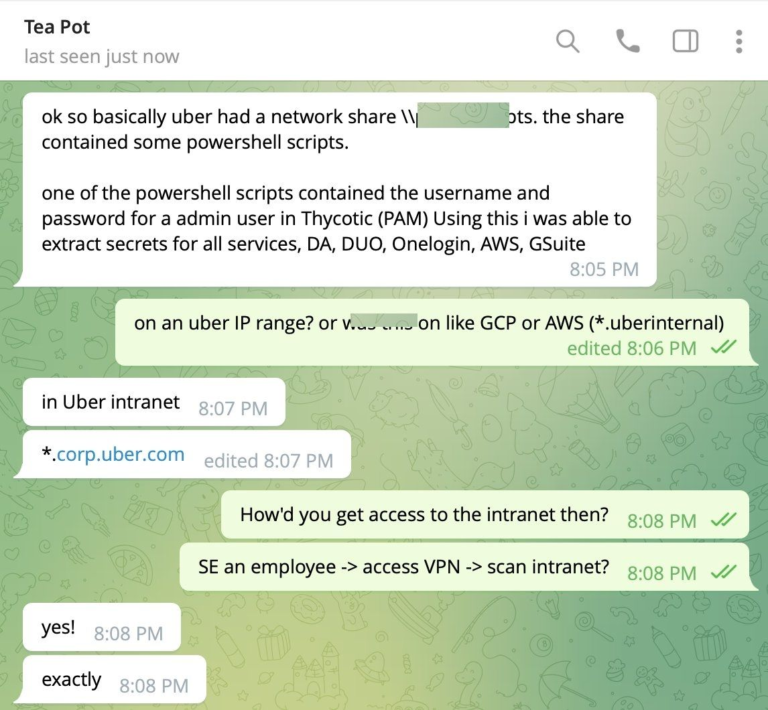
Exchanges between the attacking hacker and another hacker. Thycotic is a tool used to manage access rights for internal applications at Uber. The hacker used this tool as a pivot to access the rest of the group’s applications.
Hacker’s profile and motivations #
Based on multiple sources and our clues, the hacker’s profile seems quite consistent. It appears to be a young man who wanted to create a buzz around his achievement. He himself claimed to have done it for fun and found the company’s security weak. The hacker’s intrusion could cost him many years in prison for a brief moment filled with adrenaline.
Key takeaways #
The Uber case perfectly illustrates some security points to consider. In particular, the need to train against manipulation techniques. Once awareness has been raised, regular refreshing of current practices is crucial.
But also the dangers of leaving secrets in an administration script, especially if it is easily accessible. There are other methods of secret management.
Conclusion #
This attack sequence is a good case study. It shows the unfolding of a method that is simple in substance, yet devilishly effective. Security solutions did not detect the attack. The impersonation of an administrator perfectly succeeded in circumventing the measures in place.
Faced with this type of threat, we all feel concerned and keep a thought for the teams still in crisis.
The company is going through yet another crisis, to the point where some internet users quickly came across job postings for high-level positions in Uber’s security teams.
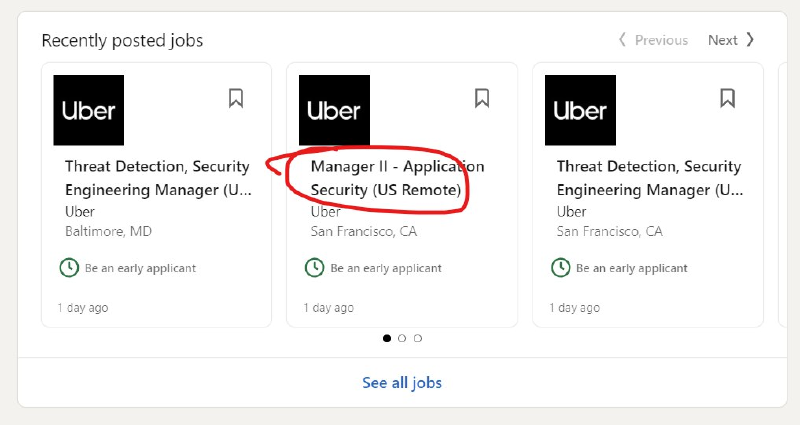
Clearly, some employees have been the scapegoats in the operation.
Thank you for reading to the end, we hope you enjoy this investigation as much as the passion we have put into it.
And thanks to my favorite proofreaders Nicolas, Sébastien, and Quentin 📝
Sources #
- Uber – Data breach 2016
- The Guardian – Uber’s ex-security chief faces landmark trial over data breach that hit 57m users
- CISO Mag – Uber Eat Data Breach 2020
- Cyble – Uber Eat leaked on darkweb
- Corben Leo – 2FA bypass
- Group-IB – Screenshots analysis
- Katie – Hardcoded powershell
- Tuan Anh Nguyen – Uber security team linkedin